
What's on this page:
- How to Educate Employees About Social Media Security
- Two-Factor Authentication and How to Set It Up on LinkedIn
- Establish a Communications Channel
- Managing Your CEO’s Social Media Account Securely
- How Employee Social Media Content Can Impact Company Security
- Security Essentials for Social Media Software
- How DSMN8 Keeps Your Employee Advocacy Program Secure
- Social Media Checklist for Employees
One of the most important things to consider when starting an employee advocacy program is security.
Whether you’re using software like DSMN8, or running a program manually, there will be security and safety measures you’ll need to factor in.
When employees use social media in the workplace, they need to understand how to be responsible and reduce the risk of cyber security threats.
In this post, we’ll outline the security essentials for any employee advocacy program, what employees need to know, and the security features an employee advocacy platform or tool should have.
How to Educate Employees About Social Media Security: What They Need to Know
All employees must understand how to keep their social media accounts secure, reducing the risk of hacking.
From setting up two-factor authentication and using a unique strong password to reviewing any apps with third-party access, make sure that your team is following social media security best practices.
Most employees know about phishing scams that occur via email, but they need to be aware that these take place on social media too.
Advise your team to never click on a link from an unknown source, and take extra caution when links are sent to them in private messages or ‘DMs’.
Employees should also be made aware that hacking can happen through social engineering, not just from not having a secure password or clicking on a suspicious link. Someone may strike up a conversation in an attempt to find out personal information, such as your mother’s maiden name or the name of your first pet.
The answers to these questions are often used as security authenticators for social media accounts, so be careful when sharing anything personal.
Social Media Security Reminders for Employees
Whether you’re starting an employee advocacy program or your colleagues are already sharing content on social media, every participant should review their account settings and security best practices.
Below are the essential security tasks and reminders each employee should follow.
We’ve also turned this into a handy checklist to make this easy. Simply download the PDF at the end of this post and share it with your colleagues.
- Use unique, strong passwords for each social media profile.
- Review your privacy settings.
- Ensure your recovery email and/or phone number is correct.
- Set up 2-factor authentication.
- Make sure that you have access to your backup email address.
- Check logged in sessions to make sure they are all you. If not, report to the social media platform and change your password.
- If using any tools like social media schedulers, check their security and data policies.
- Before clicking links in emails from social media platforms, check that the URL is correct, e.g. LinkedIn.com
- Never share your password with anyone.
- Change your password when prompted to do.
- Be wary of messages from people you don’t know, especially if links are included.
- Avoid using free public WiFi to access your social media accounts. These can be more vulnerable to hacking.
Two-Factor Authentication and How to Set It Up on LinkedIn
Two-factor authentication (2FA) is a security method to help protect your accounts from cyber criminals.
When you log in from a new device or location, your account will require a code sent to you via text message or an authenticator app such as Microsoft Authenticator.
This makes it much less likely for your social media to get hacked. Even if someone knows your password, they won’t necessarily have access to your phone or authenticator app.
Here’s how to set it up on LinkedIn:
- Install an authenticator app, e.g. Microsoft Authenticator.
- Click on ‘Settings & Privacy’. You can find this in the menu after clicking on your profile picture.
- In the ‘Sign-in & security’ section, enable ‘two-step verification’.
- Choose ‘Authenticator app’ and enter your LinkedIn password.
- Open the authenticator app on your phone and click ‘add account’ or ‘+’.
- Select ‘Other’ and use ‘LinkedIn’ as the account name.
- Enter the secret key from LinkedIn into your authenticator app.
- Verify your device by entering the 6-digit code generated by your authenticator app into LinkedIn.
For more guidance and troubleshooting, visit LinkedIn’s 2FA support page.
Establish a Communications Channel
If an employee finds their social media account hacked, contacting the social media network support team should be the first point of contact. But if they’re a brand ambassador or employee advocate, your organization needs to know too.
In this scenario, the risk must also be shared with your IT and legal teams. Whether it’s potential confidential LinkedIn conversations getting leaked, or even a hacker posing as an employee, a hacked account could be a threat to your organization.
Establish a process for passing this information on, in case of any red-flag situations.
Create a communications channel for your employee advocates to share any concerns or issues they have. Make it clear that no question is too silly!
This opens a dialogue, creating a culture where employees are provided with the support they need to safely thrive on social.
How To Manage Your CEO’s Social Media Account Securely
It’s common practice for marketing teams to manage an executive’s social media presence, especially the CEO.
But who has access to their accounts? How often is the password changed? Where is the password stored?
You should know the answers to these questions.
Review any third-party tools that have access to your CEO’s social media accounts, and remove any that are no longer used.
Take the same approach with employees. Does everyone in your marketing team need access, or can it be limited to just the person posting and engaging on their account?
If you’re using an external marketing agency or freelancers to manage your leadership team’s social media presence, this adds another layer of risk. Pay close attention to how Facebook page access is granted to avoid unnecessary complications later.
DSMN8 has an ‘executive influence’ feature that makes managing your C-Suite’s LinkedIn profiles simple.
There’s no need to share your CEO’s password with your marketers or external parties – simply connect social accounts securely and post content on their behalf with ease.
How Employee Social Media Content Can Impact Company Security
Now we’ve established how employees keep their social media accounts secure, let’s move on to the content they’re sharing on social media.
While encouraging employees to share original content is great, they must be informed about what is okay to share and what isn’t.
Revealing any confidential company information is an absolute no, and any content that includes their colleagues needs their consent before posting.
A lot of this can be considered ‘common sense’, but to be sure, outline this in your social media policy and/or guidelines.
Remind employees that most security breaches are accidental, so they need to be careful with what they’re sharing.
For example, if taking a picture of their desk to share on LinkedIn, employees should check that no confidential information is visible on their computer screen.
Providing social media training also helps to alleviate this risk, and gives employees the chance to ask any questions they may have.
Watch the podcast episode below to find out how Maike Jansen, employee advocacy lead at Dentsu Benelux, manages brand safety and security in their employee advocacy program:
Security Essentials for Social Media Software
We’ve covered the essential social media security protocols that every employee should follow.
But security goes beyond individual employee behavior. You’ll need to evaluate which tools or platforms your organization and employees are using.
Your marketing team may be using software to schedule content on the CEO’s LinkedIn account. You should know the answers to these questions:
- What access does that tool have?
- What measures do they take to ensure the security of their accounts?
- What are they doing with your data?
- Are they following laws like GDPR?
Best practice is to get your IT team involved in evaluating all software that requires access to social media accounts, including employees and corporate channels. This way you can be confident that these tools are adhering to the laws in your region, and keep your data safe.
Security Features Your Employee Advocacy Platform Should Have
An employee advocacy platform serves the purpose of getting content to your employees and enabling them to share it easily on social media.
By nature, this means the platform will need to connect to employee social media accounts.
The last thing you’ll want is to put your employees in harm’s way, so a thorough audit of any employee advocacy software’s security policies is essential.
Here’s what to look out for:
- Where and how their data is stored.
- The security certifications they hold.
- Whether they regularly conduct security audits, tests, and scans.
- If they have an up-to-date privacy policy, compliant with regulations like GDPR.
- Does the company has dedicated employees focused on security and data privacy?
- Web application architecture and implementation: does it follow OWASP guidelines?
How DSMN8 Keeps Your Employee Advocacy Program Secure
Here at DSMN8, we make security a priority at all levels of our organization.
With industry-leading compliance, DSMN8 has an ISO 27001 certification, audited by an independent body.
Our privacy & security team includes a Data Protection Officer (DPO), Chief Information Security Officer (CISO), and a Compliance Officer, who continuously ensure that DSMN8’s practices and products comply with GDPR and similar regulations.
The platform is hosted with Amazon Web Services (AWS) facilities in Europe, the most secure cloud computing environment.
Our web application follows OWASP guidelines, and our engineers participate in code security training annually. Design of all new product functionality is reviewed by its security team, and code development follows a documented SDLC process with mandatory reviews.
Additionally, we regularly conduct third-party network vulnerability scans, require strong passwords, and offer Single Sign On (SSO).
You can trust that your data and content is safe with us.
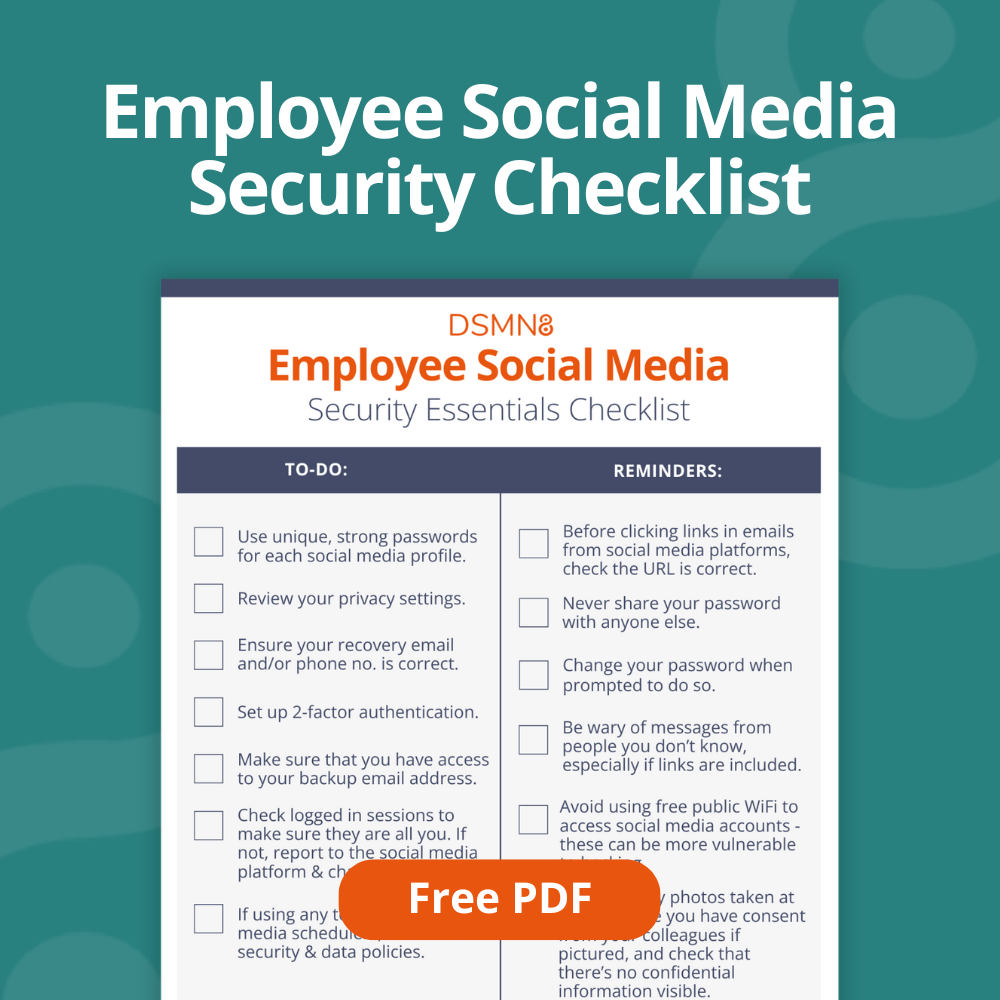
Social Media Checklist for Employees
To make things as easy as possible, we’ve created a social media security checklist for employees.
It includes ‘to-dos’ for your team to make sure their account security is up-to-scratch, and some reminders for staying safe on social.
Fill out the form below to download the PDF.
Additional Resources
Emily Neal
Emily is SEO Lead at DSMN8. She focuses on organic growth strategy across search and AI search and co-authors DSMN8's original research, including the Employee Advocacy Benchmark Report and edited CEO Bradley Keenan's book. Her background spans SEO strategy, technical web, long-form content, digital PR, and marketing automation.



